I like personality tests. A lot. From Clifton Strengths, the Big Five, and Myers-Briggs, to the cheesy ones on Facebook that share too much of my personal information back with dubious app creators—there is something to love about all of them. No matter the test, some traits are common across all my results. I am introverted, highly conscientious, and a learner. In fact, collecting and archiving information and continuously trying to improve are chief among my key personality traits.
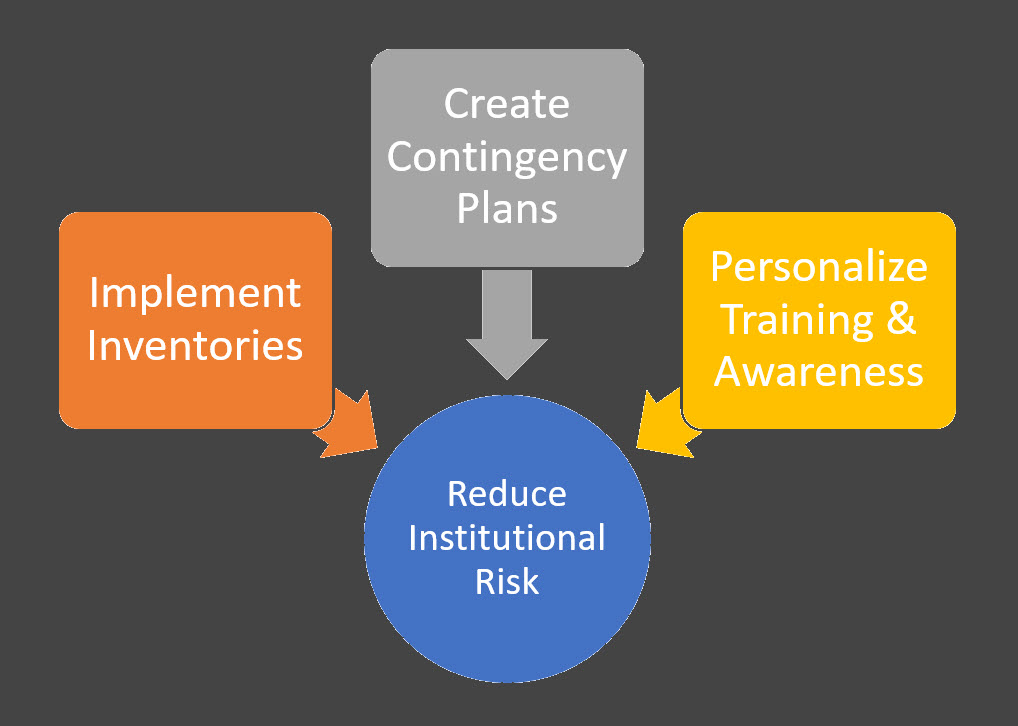
It’s in that spirit of learning and continuous improvement that I share observations from my information security consulting practice. Much of my consulting practice includes conducting information security controls assessments at colleges and universities. Three topics keep rising to the top of the actionable advice that I share with my clients after each assessment:
- Inventories
- Contingency planning
- Training and awareness
Inventories are Indispensable
It’s an information security cliché: You cannot protect that which you do not know about. It’s also true. Creating an inventory, or documenting your critical institutional information resources, data, and the processes that rely on those resources and data is hard work. Yet, such inventories are essential to a fully functioning information security program. They are needed to make sure security controls are implemented efficiently and effectively, and they are crucial for contingency planning activities like incident response and disaster recovery.
Inventories are so important that we have written about them before. Inventories don’t have to be an all-or-nothing proposition. You can create them in stages. Start with documenting your critical IT systems (ERP, LMS, CRM systems and associated physical assets), and then move on to your critical data and processes. You can use spreadsheets to maintain your inventories or use software programs.
Create Contingency Plans
Speaking of contingency planning, Benjamin Franklin provides us with our next piece of advice: “By failing to prepare, you are preparing to fail.” Most often we find that we need to recommend that institutions put in place an information security incident response plan, and we often recommend that the IT organization work on a business continuity/disaster recovery plan also.
Information security incidents are incidents that compromise the confidentiality, integrity, or availability of institutional IT resources or data. Incident response plans help ensure the secure operation of college or university information resources, minimize the negative consequences of information security incidents, and improve the institution’s ability to promptly restore operations affected by information security incidents. Failure to have an incident response process to ensure that potential information security incidents are handled promptly can subject the institution to regulatory (did someone say breach notification?), financial, and reputational risk.
Business continuity/disaster recovery plans help institutions (or units within the institution, like the IT organization) withstand business interruption events and … well … disasters. These types of plans are essential to the institution being able to fulfill its mission and daily business operations if some sort of event disrupts those operations. These plans can be developed at both the institutional level (as part of an enterprise risk management or safety function) and the unit level.
We have noticed a couple of things with business continuity/disaster recovery plans. First, they are often out of date. Remembering to update these plans as the institution changes are important. Second, as institutions move IT infrastructure, platforms, and services to the cloud, we need to do a better job of documenting data integration and synchronization processes because these transformations are largely unaccounted for in contingency plans. Business and technical teams need to work together to ensure that continuity and disaster recovery plans are revamped and tested to keep pace with the evolving technical landscape.
Personalize Training and Awareness
Past EDUCAUSE research has shown that the majority of data breaches in higher education are a result of human error. Industry research also points to human error being a factor in information security incidents and data breaches. Ensuring that institutional faculty and staff members know how to protect institutional IT resources and data, which can only be accomplished through a comprehensive information security training effort, is essential to reducing information security risk.
Yet, we often find that institutions don’t have information security training and awareness functions or the training that is provided isn’t tailored to a faculty or staff member’s role. For instance, faculty and research staff need information security awareness training that is tailored to their academic and research activities. IT personnel with elevated privileges and responsibilities might also need specialized information security training. While basic information security hygiene training is necessary for all campus community members, having tailored training for community members with specialized information security needs helps create a culture of shared responsibility for information security.
My goals in completing an information security controls assessment are to present results in a way that accurately reflect my client’s current information security state and provide actionable advice that helps my clients move their programs forward and decrease institutional information security risk. Institutions can make great headway in reducing risk by implementing inventories, creating contingency plans, and personalizing their information security training and awareness activities.
This blog was authored by Associate Vice President Joanna Lyn Grama, JD, CISSP who advises clients on information security policy, compliance, governance, and data privacy issues as part of Vantage’s Strategic Planning and Technology Management practice. Joanna is an INTJ according to Myers-Briggs, and her top Clifton Strengths are Learner, Input, and Achiever.